Continuous Security Monitoring Guide: Protecting Blockchain and Digital Assets
Waiting for a quarterly security audit to find a hole in your system is like checking if your front door is locked once every three months. In the world of blockchain and decentralized finance, where transactions happen in milliseconds and exploits can drain millions in a single block, that kind of delay is fatal. If a smart contract has a vulnerability, a bot will find it and exploit it long before your next scheduled scan. This is why continuous security monitoring has shifted from being a "nice-to-have" to a survival requirement.
| Feature | Traditional Assessments | Continuous Monitoring (CSM) |
|---|---|---|
| Frequency | Periodic (Quarterly/Annual) | Real-time / Ongoing |
| Detection Speed | Days or Weeks after incident | Immediate / Seconds |
| Approach | Reactive (Point-in-time) | Proactive (Always-on) |
| Compliance | Manual checklists | Automated evidence collection |
What Exactly is Continuous Security Monitoring?
At its core, Continuous Security Monitoring is an automated, real-time approach to maintaining ongoing awareness of information security, vulnerabilities, and threats . Instead of a snapshot in time, it provides a live movie of your security posture. For blockchain projects, this means constantly watching the network, the smart contracts, and the infrastructure for any sign of trouble.
This methodology is heavily backed by NIST SP 800-137, which provides the structured framework for Information Security Continuous Monitoring (ISCM). It tells organizations that they shouldn't just set up security controls and forget them; they need to monitor those controls to ensure they are actually working as intended. In a blockchain context, this could involve monitoring for "flash loan" attack patterns or sudden, unusual spikes in contract interactions that suggest a bug is being exploited.
The Real-World Value of Staying Alert
Why spend the resources on a continuous system? Because the cost of a breach in the crypto space is usually total. When you move from a reactive to a proactive stance, you change the game. You stop asking "What happened?" and start asking "What is happening right now, and how do we stop it?"
The biggest win is early threat detection. Imagine a scenario where an attacker finds a reentrancy bug in a DeFi protocol. In a traditional setup, you might find out via Twitter after the funds are gone. With CSM, your system flags an abnormal sequence of calls to a specific function, triggers an alert, and potentially pauses the contract automatically. You've just saved the protocol from a catastrophic loss.
Beyond just stopping hacks, this approach streamlines your operational efficiency. By automating the boring stuff-like checking if your server patches are up to date or if your API keys are leaked-your security team can focus on high-level strategy and threat hunting rather than filling out spreadsheets for an auditor.
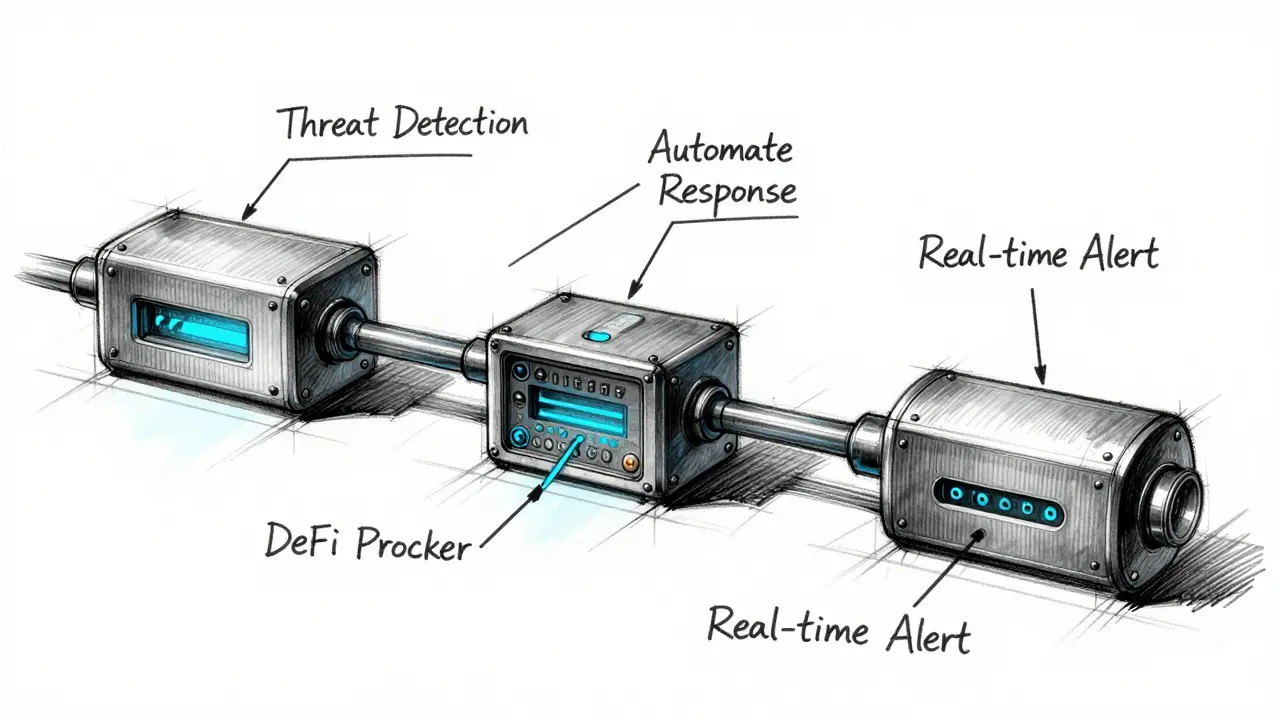
How to Implement a Monitoring Pipeline
Building a continuous monitoring system isn't about buying one single piece of software; it's about creating a pipeline that collects data, analyzes it, and acts on it. Here is how you actually build it:
- Threat Monitoring and Detection: Deploy tools that watch for anomalies. In blockchain, this means monitoring mempools for suspicious transactions or using bots to track large movements of funds from known exploiter addresses.
- Automated Response Systems: You can't wait for a human to wake up at 3 AM to stop a hack. Set up automated triggers. For example, if a specific risk threshold is hit, the system can automatically revoke permissions or trigger a "circuit breaker" in a smart contract to freeze assets.
- Continuous Control Monitoring: Regularly check your security guards. Are your firewalls actually blocking the right ports? Is your multi-sig wallet still requiring three out of five signatures? If a control fails, you need to know immediately, not during next year's audit.
- Real-time Alerting: Create a tiered alerting system. A "Low" alert might go to a dashboard, but a "Critical" alert should ping the security team's phones via PagerDuty or Telegram immediately.
Managing Risk with Data, Not Guesses
Most companies manage risk by guessing. They think, "We probably won't get hit by a 51% attack because our hash rate is high." Continuous monitoring replaces these guesses with data. By evaluating your attack surface constantly, you can assign a real-time risk score to different parts of your infrastructure.
For instance, if you see an increase in failed login attempts on your validator nodes from a specific geographic region, your risk score for "Unauthorized Access" spikes. You don't have to wait for a breach to happen to know you're being targeted; you can see the attack forming in real-time and adjust your defenses accordingly. This aligns perfectly with Cybersecurity Risk Management principles by focusing resources where the actual danger is highest.

Staying Compliant Without the Headache
If you are operating in a regulated environment, you're likely dealing with GDPR, HIPAA, or PCI DSS. Usually, compliance is a nightmare of gathering screenshots and logs once a year. CSM turns compliance into a background process.
By continuously tracking your security controls, you generate a living audit trail. Instead of scrambling to prove that you've been managing user permissions for the last twelve months, you simply pull a report from your monitoring tool that shows a continuous history of access reviews. It turns a stressful two-week audit process into a simple data export.
Does continuous monitoring replace the need for a security audit?
No. An audit is like a deep-dive health checkup by a specialist; continuous monitoring is like wearing a heart monitor. You need the audit to find deep logic flaws in your code that a monitor might miss, but you need the monitor to ensure that the environment around that code remains secure every single second.
Will this slow down my blockchain network performance?
If implemented correctly, no. Most CSM tools operate "out-of-band," meaning they analyze copies of logs or monitor the chain from a separate node. They don't sit in the middle of the transaction flow, so they don't add latency to your users' experience.
What is the most common mistake when setting up CSM?
"Alert Fatigue." Many teams set up too many alerts for minor things. When your phone pings 200 times a day for insignificant events, you'll eventually ignore the one alert that actually matters. The key is to tune your alerts so that only truly actionable events trigger a notification.
How does this help with identity-related risks?
CSM tracks user behavior and access patterns. If an admin account suddenly logs in from a new country and starts changing critical system permissions at 3 AM, the system flags this as an identity anomaly. This allows you to kill the session before the attacker can do any real damage.
What's the difference between CSM and a SIEM?
A SIEM (Security Information and Event Management) is a tool that collects and analyzes logs. CSM is a broader strategy. You might use a SIEM as one of the primary tools to achieve continuous security monitoring, but CSM also includes the policies, the automated responses, and the constant review of security controls.
Next Steps for Your Security Strategy
If you're just starting, don't try to monitor everything at once. Start with your most critical assets-your private keys, your smart contract state, and your admin access points. Set up basic alerting for these, then gradually expand your coverage to include network traffic and system logs.
For those already in the game, look into "Chaos Security Engineering." Try intentionally triggering a security alert in a test environment to see if your monitoring system actually catches it and if your team knows how to respond. The only way to know your monitoring works is to test it before a real attacker does.


Heather Warren
April 9, 2026 AT 15:40This is such a great breakdown of the differences between traditional and continuous monitoring! I think a lot of people in the DeFi space would benefit from simplifying their alerting tiers to avoid that burnout mentioned at the end.
7stargee Emmanuel Obani
April 9, 2026 AT 19:50Imagine thinking a few bots can save your money lol 🤡
Carroll Foster
April 10, 2026 AT 10:15Oh sure, because adding more automated circuit breakers won't just create a new attack vector for some genius to exploit through the governance layer. Absolute peak efficiency right there!
Aaliyah BROTHERS
April 11, 2026 AT 14:01WAKE UP PEOPLE!!! These "monitoring tools" are just more ways for the globalist shadow-governments to track every single wei moving on the chain!!!! It's a total trap!!! Why do we trust these NIST standards when they're probably written by the same ghouls trying to destroy our sovereign American currency??? ABSOLUTELY DISGUSTING!!!!
Jessie Tayaban
April 13, 2026 AT 04:24OMG i tried setting up a basic bot last week and it totally crashed my node... i was so paniced i thought i lost everything!! 😱 the struggle is so real with these setups
Jason Davis
April 15, 2026 AT 02:14Good point on the out-of-band monitoring. A lot of ppl forget that you can just run a read-only node for your monitoring pipeline so you dont lagg the main networrk.
ssjuul z
April 15, 2026 AT 07:55Exactly! Keeping the monitoring layer separate is key to maintaining performance while staying safe. Let's keep pushing for better open-source tools for this! 🚀
Rima Dinar
April 16, 2026 AT 19:53I really believe that if we approach this with a mindset of continuous growth and mentorship, we can help the newer developers understand that security isn't just a checkbox you tick at the end of a project, but rather a living, breathing part of the development lifecycle that requires constant attention and a lot of patience as you refine your alerting systems over time to avoid the dreaded alert fatigue.
Hope Johnson
April 17, 2026 AT 14:35When we consider the ethical implications of automated response systems, we must ask ourselves if we are trading human judgment for algorithmic efficiency in a way that might inadvertently marginalize legitimate users during a false positive event. It is a profound philosophical tension between the need for immediate protection of digital assets and the inclusive ideal of a decentralized network where no single automated 'kill switch' can override the collective intent of the community without transparency and rigorous oversight.
Prasanna Shembekar
April 19, 2026 AT 01:20too many alerts lol
aletheia wittman
April 20, 2026 AT 00:58wait so like... if my phone pings 200 times i just ignroe it?? that sounds like a nightmare lol i would literally throw my phone across the room
Emily H
April 21, 2026 AT 13:20The distinction between a SIEM and a CSM strategy is quite pertinent. One provides the data, while the other provides the operational framework necessary to act upon that data effectively.
Swati Sharma
April 22, 2026 AT 22:05I totally agree with the focus on the mempool for threat detection. Implementing a robust Heuristic Analysis on pending transactions can help identify front-running bots or flash loan attacks before they are even mined into a block, which is the essence of a proactive security posture.
Mikayla Murphy
April 23, 2026 AT 17:09It's really important to remember that behind these technical controls are people whose livelihoods are at stake when a protocol is drained. The human element of security is just as vital as the automated pipelines.
Stanly Hayes
April 24, 2026 AT 11:04SURE, just automate everything and hope the AI doesn't decide to freeze your funds by mistake! Great plan!
Chidinma Sandra okafor
April 25, 2026 AT 10:42Typical. We build these fancy systems but the actual governance is still a joke. Maybe if we spent less time on 'pipelines' and more time on actual decentralization we wouldn't need a heart monitor for every single contract. But hey, keep trusting the machine! 🙄
Agnessa Dale
April 26, 2026 AT 05:22This is a very helpful guide for anyone getting started with blockchain security!
Kelly Cantrell
April 27, 2026 AT 23:08The NIST framework is just another way for the federal government to get a backdoor into our private keys. If you think these 'standards' are for your protection, you're dreaming. It's all about surveillance and control under the guise of 'security' and 'compliance'. Stay vigilant and keep your keys offline.